
Security Compliance Services
Comply with Cyber Security requirements legal or regulatory, from internal or external parties.
-
Identify missing gaps.
-
Implement missing controls.
-
Get guidance to stay compliant.

Comply with Cyber Security requirements legal or regulatory, from internal or external parties.
Identify missing gaps.
Implement missing controls.
Get guidance to stay compliant.
Security compliance requirements can pop up from various angles. Sometimes it's internal, a regulator, the government, a vendor or some third-party that needs your company to comply.
Non-compliance hinders a business goal being achieved.
Your company might be fined or face penalties and other consequences.
Non-compliance can make the company look bad to both internal and external stakeholders.
Understand, assess and achieve security compliance goals. Maintain a positively sharp image with applicable local and international laws, regulations, parent companies and third-parties.
Get a clear report of gaps in compliance with requirements.
Become compliant, so your company can meet its strategic goals.
Minimise penalties, the risk of fines and reputational damage.
Bring your own requirements and we'll support.
It doesn't matter the requirements are custom-built or from an existing and well-known framework or standard.
Become compliant.
Identify gaps between your current security operations and your compliance requirements.
Align your organisation's operations to an internationally respected framework.
Keep your security operations in check and robust to protect against cyber attacks.
Start seeing results within 24 hours.
Complete the form below to request a quote from our sales team. We will respond to you within 24 hours.
Digitally sign our proposal and submit payment online. We accept credit cards and wire transfers.
We will host a kick-off meeting with your team to agree on the next steps and to get started on the project.
Take the next step to protect your enterprise's IT network and data.
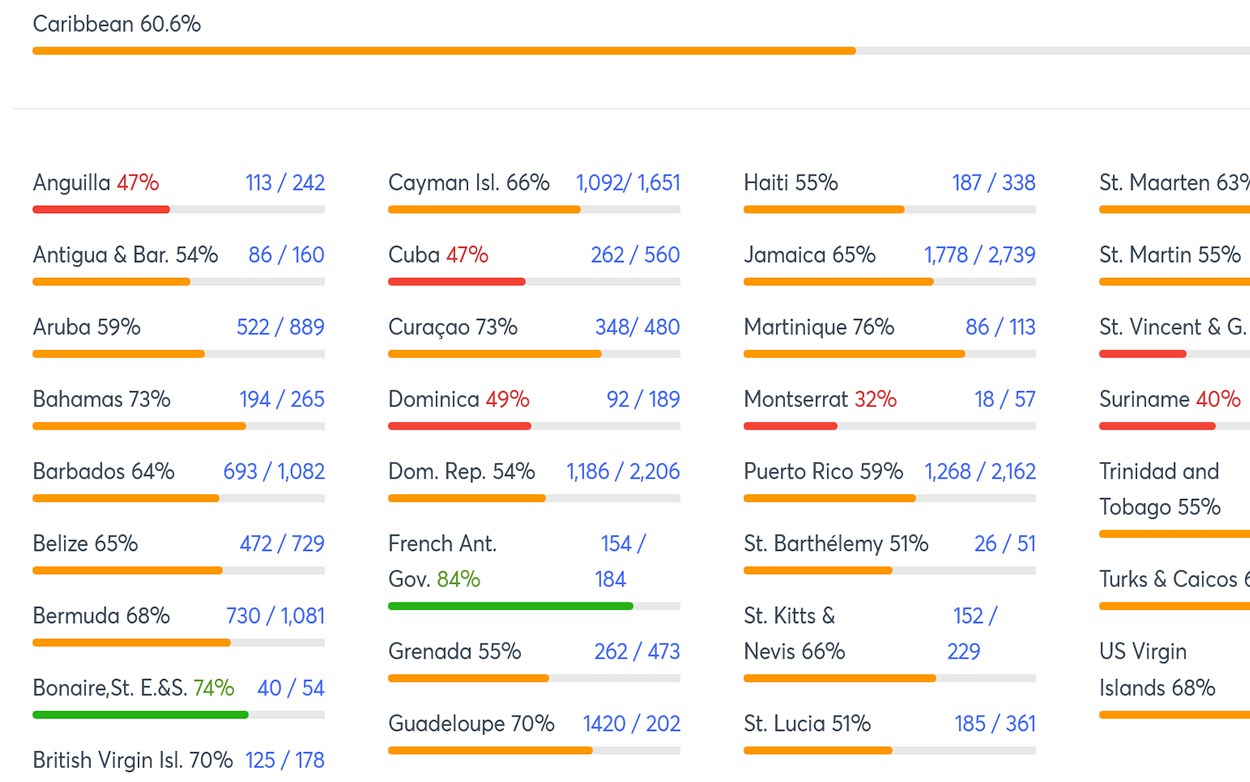
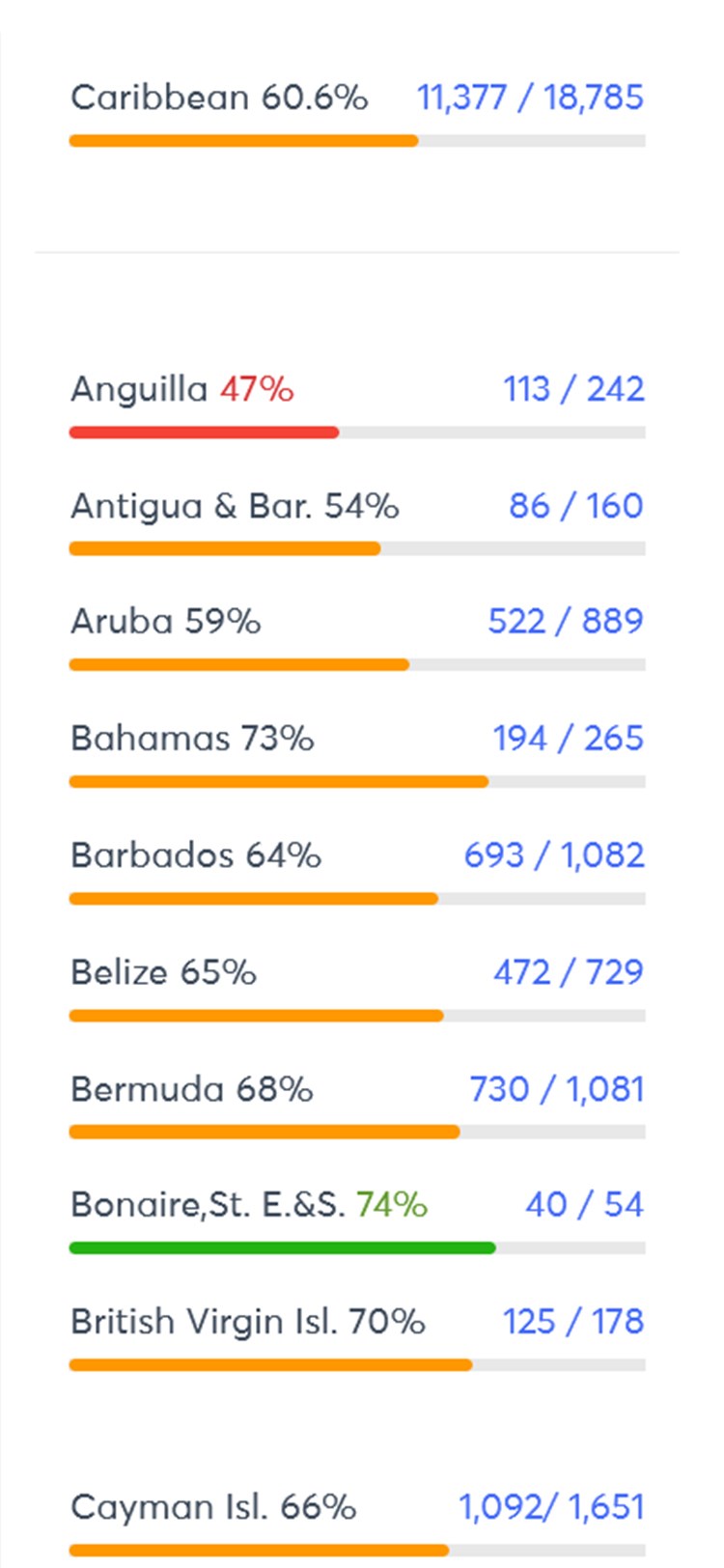
Each month we analyse over 18,000 Caribbean domains to provide usage statistics on HTTPS and Security Headers.
Below are some related services you might also be interested in. Request a quote today.
Check for vulnerabilities across your internal and external network.
Click hereDirectly analyse your configuration files for security vulnerabilities.
Click hereAssess your web app's functionality for security vulnerabilities.
Click here
Start seeing results in 24 hours.